PaperCut NG allows for unauthenticated XMLRPC commands to be run by default. Versions 22.0.12 and below are confirmed to be affected, but later versions may also be affected due to lack of a vendor supplied patch.

All posts in "Exploits And POCs"
- September 28, 2023
A vulnerability was found in PlayTube 3.0.1 and classified as problematic. This issue affects some unknown processing of the component Redirect Handler. The manipulation leads to information disclosure. The attack may be initiated remotely. The identifier VDB-238577 was assigned to this vulnerability. NOTE: The vendor was contacted early about this disclosure but did not respond
- September 23, 2023
<a href="https://system32.ink/cve-2023-0099-exploit-simple-urls-115-reflected-xss/" data-title="CVE-2023-0099 Exploit : Simple Urls CVE-2023-0099 Exploit : Simple Urls < 115 - Reflected XSS
Description The Simple URLs WordPress plugin before 115 does not sanitise and escape some parameters before outputting them back in some pages, leading to Reflected Cross-Site Scripting which could be used against high privilege users such as admin.
<a href="https://system32.ink/cve-2023-0099-exploit-simple-urls-115-reflected-xss/" aria-label="CVE-2023-0099 Exploit : Simple Urls Read More - September 20, 2023
<a href="https://system32.ink/cve-2023-0255-mass-exploit-wordpress-enable-media-plugin/" data-title="CVE-2023-0255 Mass Exploit WordPress CVE-2023-0255 Mass Exploit WordPress < Enable Media Plugin
Mass Exploit – CVE-2023-0255 < WordPress < Enable Media+Plugin < Unauthenticated Arbitrary File Upload Dork : inurl: wp-content/plugins/enable-media/ Infected Sites : 600K WordPress Sites
<a href="https://system32.ink/cve-2023-0255-mass-exploit-wordpress-enable-media-plugin/" aria-label="CVE-2023-0255 Mass Exploit WordPress Read More - September 15, 2023
This is a Proof of Concept (PoC) for CVE-2023-3244, a vulnerability in comment-like-dislike. The PoC demonstrates the exploitability of this vulnerability and serves as a reference for security researchers and developers to better understand and mitigate the risk associated with this issue.
- September 15, 2023
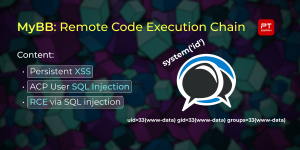
In MyBB 1.8, templates rely on HTML code with basic references to PHP variables, rendered by executing them as PHP code (eval()). This limitation is enforced through regular expression-based validation (performed during the importing of themes, and modification of individual templates). However, the validation process did not account for runtime errors related to regular expression
- September 15, 2023
Slient Url Exploit New Cve Chrome Exploit Html Downloader Put Your Link URL Infection (Silent Java Drive By) URL Infection Exploit Silent Java Drive by downloads may happen when visiting a site, opening an e-mail message. It may even happen by clicking on a malicious pop-up window: by clicking on the window in the belief
- September 14, 2023
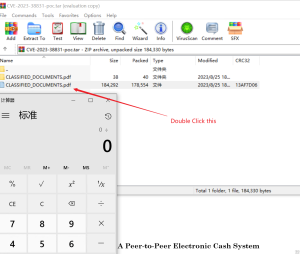
It’s an introduction on how to set up CVE-2023-40930 Repetition Enviroment Learn more about this CVE problem in “issue detail.pdf”
- September 13, 2023
CVE-2023-36844 , CVE-2023-36845 , CVE-2023-36846 , CVE-2023-36847A Proof of Concept for chaining the CVEs to achieve Remote Code Execution in Juniper JunOS within SRX and EX Series products.
- September 9, 2023
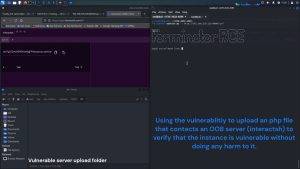
RCE Exploit for WordPress Plugin Media-Library Plugin < 3.10 (CVE-2023-4634) Info Patrowl discovered An unauthenticated RCE Vulnerability on Media-Librairy-Assistant WordPress Plugin in version < 3.10. The exploit is not trivial and requires just a little setup explained bellow. Global discover and exploitaiton of the exploit could be found in our blog: https://patrowl.io/blog-wordpress-media-library-rce-cve-2023-4634/ Prerequisite of exploitaiton Detection
- September 4, 2023
A critical vulnerability has been discovered in the WordPress plugin Forminator, which enables an unauthorized attacker to upload arbitrary files to a server. The initial proof of concept (PoC) was poorly written, the original researcher shared a few unclear screenshots along with a request containing unexplained code. So I wrote a python script to simplify
- September 4, 2023
VMWare Aria Operations for Networks (vRealize Network Insight) Static SSH key RCE (CVE-2023-34039) VMWare Aria Operations for Networks (vRealize Network Insight) from version 6.0 to 6.10 did not regenerate the ssh keys for the support and ubuntu users, allowing an attacker with SSH access to gain root shell access to this product
- September 2, 2023
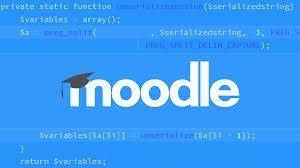
This repository contains combined exploits for two vulnerabilities in Moodle, a widely used open-source learning management system (LMS). The exploits leverage the vulnerabilities to demonstrate Unauthenticated Arbitrary Folder Creation leading to Stored Cross-Site Scripting (XSS) and Self-XSS leading to Account Takeover. Please note that these exploits are provided for educational purposes and should not be
- September 2, 2023
Inappropriate file type control in Zscaler Proxy versions 3.6.1.25 and prior allows local attackers to bypass file download/upload restrictions. During the summer of 2022, I have found a vulnerability affecting the ZScaler proxy (versions 3.6.1.25 and prior). This vulnerability would allow local attackers to bypass the restriction on downloads/uploads of password-protected archives using tools like
- August 31, 2023
About Vcenter Comprehensive Penetration and Exploitation Toolkit | Vcenter Comprehensive Penetration and Exploitation Toolkit The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts
- August 28, 2023
Vulnerability in the Oracle Java SE, Oracle GraalVM Enterprise Edition product of Oracle Java SE (component: Swing). Supported versions that are affected are Oracle Java SE: 8u361, 8u361-perf, 11.0.18, 17.0.6, 20; Oracle GraalVM Enterprise Edition: 20.3.9, 21.3.5 and 22.3.1. Easily exploitable vulnerability allows unauthenticated attacker with network access via HTTP to compromise Oracle Java SE,
- August 28, 2023
Dork : inurl: wp-content/plugins/jupiterx-core/ A vulnerability has been found in JupiterX Core Premium Plugin up to 3.3.5 on WordPress (WordPress Plugin) and classified as critical. This vulnerability affects an unknown function. The manipulation with an unknown input leads to a unrestricted upload vulnerability. The CWE definition for the vulnerability is CWE-434. The software allows the attacker to upload
- August 28, 2023
Python 3 code to exploit a SEH based Buffer Overflow vulnerability in RaidenFTPD v.2.4.4005. This vulnerability allows a local attacker to execute arbitrary code via the Server name field of the step by step setup wizard.
- August 28, 2023
RARLabs WinRAR before 6.23 allows attackers to execute arbitrary code when a user attempts to view a benign file within a ZIP archive. The issue occurs because a ZIP archive may include a benign file (such as an ordinary .JPG file) and also a folder that has the same name as the benign file, and
- August 25, 2023
An unauthenticated path traversal vulnerability affects the “STAGIL Navigation for Jira – Menu & Themes” plugin before 2.0.52 for Jira. By modifying the fileName parameter to the snjFooterNavigationConfig endpoint, it is possible to traverse and read the file system.
- August 25, 2023
A security vulnerability in MICS Admin Portal in Ivanti MobileIron Sentry versions 9.18.0 and below, which may allow an attacker to bypass authentication controls on the administrative interface due to an insufficiently restrictive Apache HTTPD configuration.