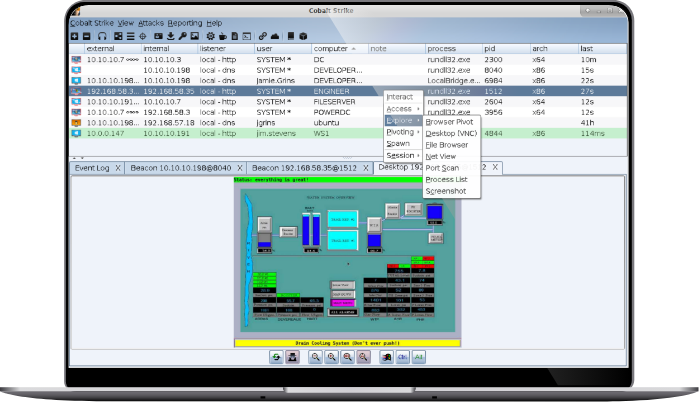
Cobalt Strike is Threat emulation software. Execute targeted attacks against modern enterprises with one of the most powerful network attack kits available to penetration testers. This is not compliance testing.
September 19th, 2023 – Cobalt Strike 4.9
- Authorization files are no longer backwards compatible.
- Changed Post-Ex DLL’s to use prepended loaders (sRDI/Double Pulsar).
Implemented in browserpivot, hashdump, invokeassembly, keylogger, mimikatz, netview, portscan, powershell, screenshot, and sshagent.
Added Aggressor hooks for applying UDRLs to post-ex DLLs (POSTEX_RDLL_GENERATE).
Added support for transform.strrep to post-ex DLL Processing.
Added post-ex.cleanup malleable C2 profile property.
Added smart-inject pointers to the POSTEX_RDLL_GENERATE hook. - Added Beacon without the exported ReflectiveLoader function to support the prepended UDRLs (sRDI/Double Pulsar).
The BEACON_RDLL_SIZE function default changed from 0 to 5k.
When the BEACON_RDLL_SIZE returns 0, then a Beacon without the reflective loader is passed to BEACON_RDLL_GENERATE and BEACON_RDLL_GENERATE_LOCAL hooks. - Added Beacon User Data to pass user specified information via UDRL.
Added support for syscall functions addresses/numbers.
Added a user specified field to Beacon User Data.
Added BOF API function to get the pointer to the user data. - Added data-store command to store BOFs and .NET assemblies in the beacon Data Store.
Added the aggressor script functions for supporting the beacon Data Store.
Added BOF API functions to access and protect stored items in the beacon Data Store. - Support spawning processes under the impersonated user security context.
- Added DuplicateHandle, ReadProcessMemory, and WriteProcessMemory system calls in beacon.
- Added Malleable C2 Profile definition of Host Profiles to customize the uri, header, and parameter attributes of the HTTP(S) get/post to be host specific and dynamic.
- Added callback support to aggressor script functions: bnet, beacon_inline_execute, binline_execute, bdllspawn, bexecute_assembly, bhashdump, bmimikatz, bmimikatz_small, bportscan, bpowerpick, bpowershell, and bpsinject
- Added support for a HTTP(S) beacon based on the WinHTTP library.
Added .http-beacon.library Malleable C2 setting to specify the default beacon http library type (wininet|winhttp). - Added aggressor script support for sending/receiving data between clients.
- Added BOF APIs to access the key/value store in beacon.
- Added BOF API to retrieve the sleep mask information.
- Added Malleable C2 sleep setting to match the sleep command syntax.
- Fixed Malleable C2 strrep setting issues with sleep mask BOF.
- Fixed Malleable C2 headers_remove setting.
- Fixed Malleable C2 http-config.headers setting with Content-Type option adds “Content-Type: null” header.
- Fixed c2lint syntax highlighting when data jitter and append are used.
- Fixed steal_token command to open a process that is protected.





What do you think?
It is nice to know your opinion. Leave a comment.