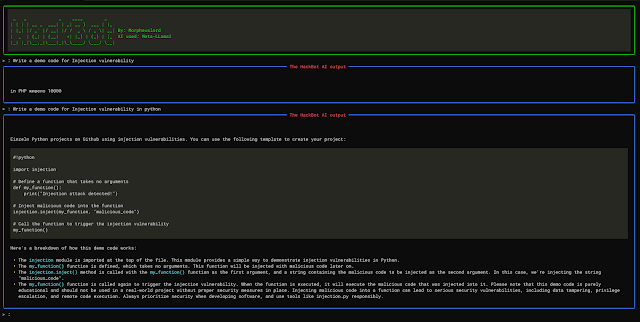
Welcome to HackBot, an AI-powered cybersecurity chatbot designed to provide helpful and accurate answers to your cybersecurity-related queries and also do code analysis and scan analysis. Whether you are a security researcher, an ethical hacker, or just curious about cybersecurity, HackBot is here to assist you in finding the information you need.
HackBot utilizes the powerful language model Meta-LLama2 through the “LlamaCpp” library. This allows HackBot to respond to your questions in a coherent and relevant manner. Please make sure to keep your queries in English and adhere to the guidelines provided to get the best results from HackBot.
Features
- Local AI/ Runpod Deployment Support: I have added an option using which you can easily deploy the Hackbot chat interface and use llama in 2 ways:
- Using RunPod: You can use runpod serverless endpoint deployment of llama and connect them to the chatbot by changing the
AI_OPTIONsection of the .env file forRunpod you need to use RUNPODand forLocal Llama deployment LOCALLLAMA.RUNPOD&LOCALLLAMA - Key Notes: For the runpod version of the llama to work you need to make sure the
RUNPOD IDand yourRUNPOD API KEYare set. - AI Cybersecurity Chat: HackBot can answer various cybersecurity-related queries, helping you with penetration testing, security analysis, and more.
- Interactive Interface: The chatbot provides an interactive command-line interface, making it easy to have conversations with HackBot.
- Clear Output: HackBot presents its responses in a well-formatted markdown, providing easily readable and organized answers.
- Static Code Analysis: Utilizes the provided scan data or log file for conducting static code analysis. It thoroughly examines the source code without executing it, identifying potential vulnerabilities, coding errors, and security issues.
- Vulnerability Analysis: Performs a comprehensive vulnerability analysis using the provided scan data or log file. It identifies and assesses security weaknesses, misconfigurations, and potential exploits present in the target system or network.





What do you think?
It is nice to know your opinion. Leave a comment.