t embeds the executable file or payload inside the jpg file. The method the program uses isn’t exactly called one of the steganography methods [secure cover selection, least significant bit, palette-based technique, etc ]. For this reason, it does not cause any distortion in the JPG file. The JPG file size and payload do not have to be proportional.The JPG file is displayed normally in any viewing application or web application. It can bypass various security programs such as firewall, antivirus. If the file is examined in detail, it is easier to detect than steganography methods.However, since the payload in the JPG file is encrypted, it cannot be easily decrypted. It also uses the “garbage code insertion/dead-code insertion” method to prevent the payload from being caught by the antivirus at runtime.
File(s)
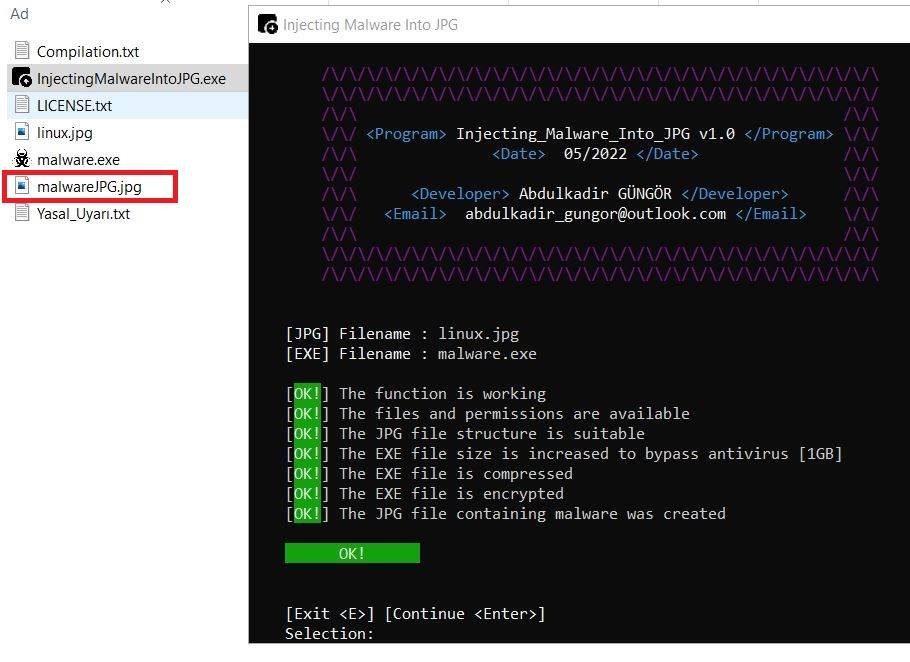
1) InjectingMalwareIntoJPG.py : It is the script that embeds the payload into the JPG file.
2) malware_v1.py : It is the script that extracts the malware in the existing image file and runs it. The malware loaded JPG file must be in the same folder. (Default JPG Name : “malwareJPG.jpg”)
3) malware_v2.py : It is the script that extracts the malware in the JPG file downloaded from the internet and runs it. (Default Url : “https://raw.githubusercontent.com/abdulkadir-gungor/JPGtoMalware/main/.image/malwareJPG.jpg”) (After the script code is compiled, the values of the variables can be seen with the static analysis of the program.)
4) malware_v3.py : It is the script that extracts the malware in the JPG file downloaded from the internet and runs it. (Default Url : “https://raw.githubusercontent.com/abdulkadir-gungor/JPGtoMalware/main/.image/malwareJPG.jpg”) (After the script code is compiled, the values of the variables can be seen with dynamic analysis of the program.)





What do you think?
It is nice to know your opinion. Leave a comment.