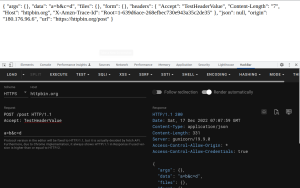
A browser extension for Penetration Testing. Available on Chrome Web Store and Firefox Add-ons. Requested Permissions

All posts tagged in "Web Tool"
- October 23, 2023
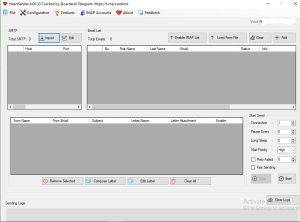
Decoding 9WOLF-S3NDER Email senderEmail To Sms Sender
- October 7, 2023
This is simple scanner for CVE-2023-22515, a critical vulnerability in Atlassian Confluence Data Center and Server that is actively being exploited in the wild by threat actors in order “to create unauthorized Confluence administrator accounts and access Confluence instances”. The vulnerability was initially described as a “privilege escalation” issue, but Atlassian later changed the classification to
- September 30, 2023
Nightmangle is post-exploitation Telegram Command and Control (C2/C&C) Agent, It was developed as Proof of Concept (POC), that Telegram API can be used by threat actors for post-exploitation and to control their agents.. Nightmangle uses Telegram as a C2 server to communicate between the attacker and the client. However, it can only set one Telegram
- September 28, 2023
An unknown hacker or a group of hackers just claimed to have hacked into “Equation Group” — a cyber-attack group allegedly associated with the United States intelligence organization NSA — and dumped a bunch of its hacking tools (malware, private exploits, and hacking tools) online.
- September 20, 2023
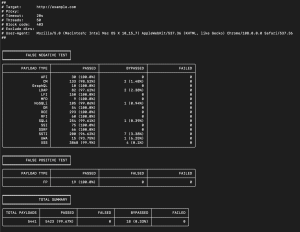
WAF bypass Tool is an open source tool to analyze the security of any WAF for False Positives and False Negatives using predefined and customizable payloads. Check your WAF before an attacker does. WAF Bypass Tool is developed by Nemesida WAF team with the participation of community. PayloadsDepending on the purpose, payloads are located in
- September 18, 2023
Heart Sender V4.00.33 New Update 2023 You Can Sent SMS from SMTP Multiple SMTP Allow Auto Rotates Features:New Advance features addBest Solution For Email SpammingCustom Subject AddedYou Can Sent SMS from SMTPMultiple SMTP AllowAuto Rotates SMTPSending based upon your leadsOffice Box sendingAWS bounce controlEmail to sms sendingAWS Access Key ControlMultiple Leads ListBulk SMTP CheckerNew Sending
- September 18, 2023
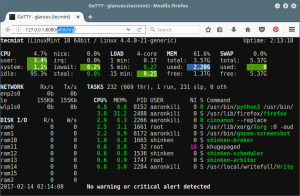
GoTTY is a simple command line tool that turns your CLI tools into web applications.You can download the latest stable binary file from the Releases page. Note that the release marked Pre-release is built for testing purpose, which can include unstable or breaking changes. Download a release marked Latest release for a stable build.
- September 15, 2023
OpenText™ EnCase™ Forensic finds digital evidence no matter where it hides to help law enforcement and government agencies reduce case backlogs, close cases faster and improve public safety. For more than 20 years, investigators, attorneys and judges around the world have depended on EnCase Forensic as the pioneer in digital forensic software to deliver reliable
- September 15, 2023
Slient Url Exploit New Cve Chrome Exploit Html Downloader Put Your Link URL Infection (Silent Java Drive By) URL Infection Exploit Silent Java Drive by downloads may happen when visiting a site, opening an e-mail message. It may even happen by clicking on a malicious pop-up window: by clicking on the window in the belief
- September 9, 2023
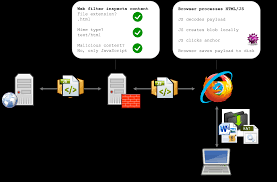
The full explanation what is HTML Smuggling may be found here. The primary objective of HTML smuggling is to bypass network security controls, such as firewalls and intrusion detection systems, by disguising malicious payloads within seemingly harmless HTML and JavaScript code. By exploiting the dynamic nature of web applications, attackers can deliver malicious content to a
- September 4, 2023
One-Click to get well-designed cross-platform ChatGPT web UI. Features Roadmap
- September 4, 2023
Shodan Query Compilation with custom scripts 🙂 Shodan gathers information by interacting with web services and this information is stored in an object called the banner, so when you search anything using a shodan dork (search query) shodan takes the information from the banner of that service and displays it to you.
- August 31, 2023
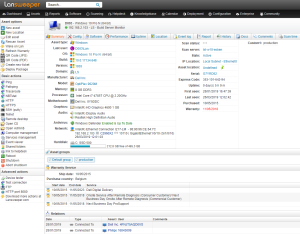
Lansweeper is an IT asset management solution that provides network discovery of all connected users, devices, and software within the IT estate. Lansweeper’s device recognition capabilities provide complete visibility across the entire IT estate, in one centralized IT inventory.
- August 30, 2023
AI tool for creating fake photos of people with many options: